on April 18, an attacker waltzes in and exploits Kelp DAO’s bridge, making off with a jaw-dropping $292 million. And guess what? This heist happened just 15 months after someone had the audacity to
actually
warn about the vulnerability. Talk about a “hold my drink” moment for DeFi!
Now, let’s get this straight: the biggest DeFi exploit of 2026 didn’t need some fancy zero-day vulnerability or a cutting-edge attack vector. Nope! It just required one little forged cross-chain message, verified by a single validator, to drain $292 million from a bridge that was already flagged as a hot mess over a year ago. Sometimes, you really can’t make this stuff up!
On that fateful day, our rogue attacker exploited Kelp DAO’s LayerZero-powered rsETH bridge, stealing a cool 116,500 rsETH. What did they do next? Why, they instantly deposited the loot into Aave as collateral and borrowed over $190 million in real WETH. Genius, right? Just a casual Tuesday for DeFi!
This little escapade resulted in a cascade of bad debt, triggering mass panic and over $10 billion in withdrawals from Aave, not to mention emergency freezes across lending protocols. And here I thought I’d seen all the drama DeFi had to offer!
What’s even more fascinating is that both LayerZero and Kelp DAO have been expertly dodging the fact that this specific attack surface had been flagged-loudly and clearly-over a year before the exploit. It’s almost like they thought ignoring warnings would make them go away.
Back in January 2025, a brave soul posted on the Aave governance forum, warning that Kelp’s 1/1 DVN (Decentralized Verifier Network) configuration was basically asking for trouble. They pointed out that a single compromised validator signature could trigger a disaster, and insisted that more DVN verifications were necessary to avoid such a calamity. Spoiler alert: they were right!
That fifteen-month gap between the warning and the actual heist? Oh, just a minor detail that makes this incident stand out from your run-of-the-mill bridge hack. This wasn’t about “unknown unknowns.” No, no! It was a well-documented vulnerability that was just ignored while Kelp was busy spreading rsETH across more than 20 blockchains like confetti at a New Year’s party.
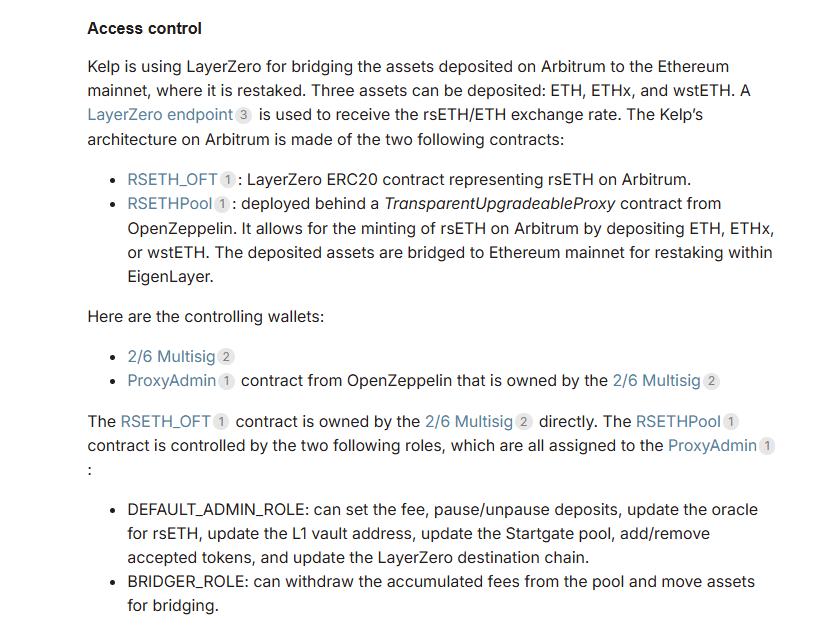
How the Attack Worked
According to LayerZero’s oh-so-insightful incident statement, the attackers managed to access the list of RPC (Remote Procedure Call) nodes used by LayerZero Labs’ DVN. Then they compromised two of those nodes, which were supposed to be independent but, as usual, turned out to be anything but. They swapped out the software with malicious binaries like a magician pulling a fast one.
These shady nodes were cleverly programmed to lie selectively. They fed forged data to the DVN while maintaining a pristine reputation with everyone else querying those nodes, including LayerZero’s own monitoring. It’s like their version of being two-faced, but in the tech world!
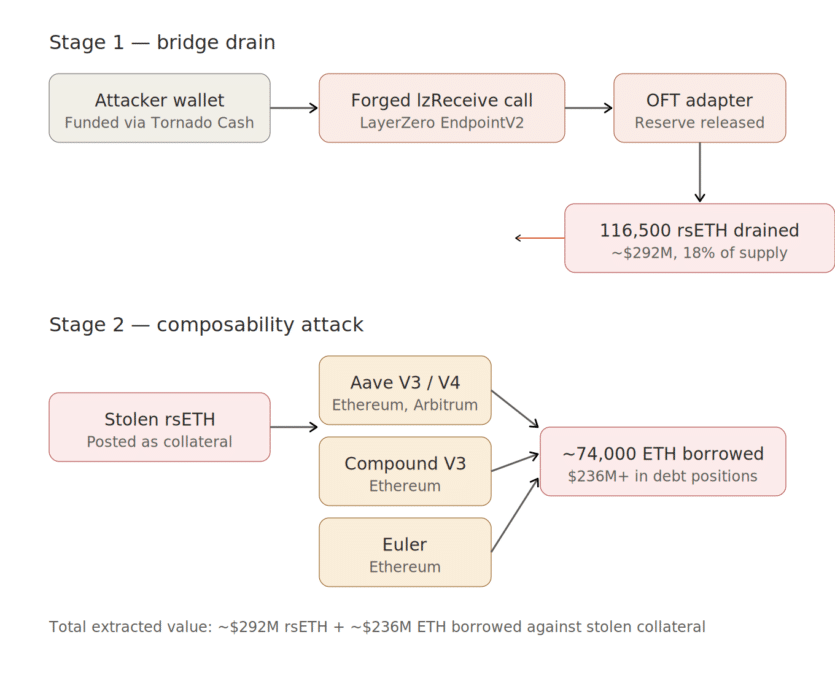
But wait, there’s more! To seal the deal, the hackers launched DDoS attacks against the uncompromised external RPCs, forcing the DVN to switch over to the poisoned nodes. Talk about a catastrophic failover!
Once that switcheroo happened, the DVN confirmed a transaction that never took place, and just like that, the bridge released 116,500 rsETH. If only they had a multi-DVN configuration (like 2/2 or 2/3), this fiasco could’ve been avoided. But who needs backup when you can live on the edge with a 1/1 setup? Right?
Kelp’s emergency pauser multisig froze contracts a mere 46 minutes after the money drain. Two subsequent attempts to pull another 40,000 rsETH (worth around $100 million) were thwarted, thanks to that timely pause. Without it, the total losses could have soared to $490 million. Now that’s what I call a close call!
The Blame Game
In its riveting post-mortem, LayerZero blamed KelpDAO for choosing the 1/1 DVN configuration despite previously communicated “best practices” about DVN diversification. They framed the incident as an application-layer failure, not a protocol-level blunder, and assured everyone that there was zero contagion to other LayerZero applications. Because, of course, it’s always someone else’s fault!
Kelp, however, isn’t taking this lying down. In a memo shared with the team, they pointed out that the 1/1 DVN setup is actually the configuration featured in LayerZero’s own V2 OApp Quickstart guide. How convenient! They also mentioned that there were no specific recommendations from LayerZero to change the rsETH DVN configuration through their direct communication channel since July 2024. Funny how that works!
Recent reports revealed that around 40% of all LayerZero applications currently run on 1/1 configurations. A Dune analysis of roughly 2,665 active LayerZero OApp contracts found that nearly half are using these minimal setups. So it seems like Kelp isn’t alone in this delightful mess!
LayerZero has since decided to stop signing messages for any application using a 1/1 DVN configuration, which means a broad migration to multi-DVN architectures is on the horizon. How noble of them!
The Structural Problem
The January 2025 Aave governance warning wasn’t just a random shout into the void. The vulnerability it described-a 1/1 DVN creating a single point of failure-is not exactly groundbreaking knowledge. It’s a known design trade-off in LayerZero’s modular architecture. Ironically, LayerZero’s own CryptoEconomic DVN Framework, launched with Eigen Labs in October 2024, was specifically designed to address this very issue. You can’t make this stuff up!
But the incentive structure pulled in the opposite direction. Under pressure to boost market share, liquid restaking protocols like Kelp opted for rapid multi-chain deployment, which is fast and cheap, instead of taking the painstaking route of configuring multi-DVN redundancy. Clearly, speed was of the essence, and who cares about security?
This led us to where we are today-a glaring example of what happens when good security practices are tossed aside in favor of expediency.
The Kelp exploit isn’t just an isolated failure; it’s a loud alarm bell about the default security standards across omnichain infrastructure. If nearly half of all LayerZero applications are using the same minimal configuration that just got exploited for $292 million, you can bet the market will start making some serious distinctions between protocols that merely claim to be “cross-chain” and those that are genuinely secure. Buckle up, folks!
Read More
- Brent Oil Forecast
- Gold Rate Forecast
- Silver Rate Forecast
- Stablecoins: The New Corporate Opium or Financial Revolution?
- How the SEC and Nasdaq Play Whack-a-Mole with Chinese IPO Scandals 🎭💼
- POWER’s 90% Crash: The Crypto Tale You Won’t Believe
- Discover the Hidden Truth Behind Snaky Way ($AKE) – You Won’t Believe This! 🐍😂
- Ethereum’s 10-Year Party: How US Immigration Accidentally Created a Crypto Giant 🎉💼
- Gold vs. Bitcoin: Which Is More Likely to Cause a Champagne Shortage?
- PENGU’s Wild Ride: Will This Memecoin Defy Fate and Multiply By 4X?
2026-04-21 16:53